Apple, one of the most admired and wanna be brands has always known for its quality products, security and the best user experience. The latest report, however, on software and app vulnerability portrays a different picture.
For as long as there has been written history, we find the tales of good guys vs. bad guys. As years rolled on and decades turned into centuries, the weapons have evolved, but the battle rages on. Midway into the second decade of the 21st century, we find ourselves embroiled in an information war. 3.17 billion people, nearly 43% of the world population, uses the Internet at an average of 21.7 hours a month. The gateway for most of these people is either desktops or smartphones. As a direct consequence of that, we see that hackers who are trying to steal our information target these two platforms specifically.
Every year, the CVE Details compile a list of publicly announced vulnerabilities and ranks software based on the frequency and threat levels of the vulnerabilities that they contain for that calendar year. Surprisingly, Apple Inc. (NASDAQ:AAPL) managed to top this year’s list with their Desktop OS topping the list, followed by iOS for the second spot. In comparison, last year Microsoft’s Internet Explorer topped the list with Mac OS X in the second place. Google Chrome, the world’s most popular browser, also managed to drop off the top 5 of this ignominious list. So what has changed in the world of security in the last year or so? And what does it mean for the average smartphone consumer as well as the corporate user? This is what our analysis focuses on for today!
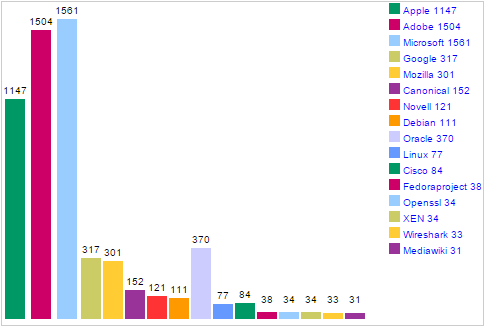
Apple, Adobe And Microsoft Tops List of Software With Most Vulnerabilities
Taking a quick glance over last year’s report, we find that there are quite a few repeat offenders in the top 5 list! Apple’s offering for the desktop and mobile had been featured at the number 2 and no 5 spots with Microsoft Corporation (NASDAQ:MSFT) at Numero Uno with the much-hated Internet Explorer. The Linus Kernel also made an appearance at the number 3 spot with the last position being picked up by Google’s Chrome browser.
This year, however, the tables have turned, and Apple finds itself occupying the top two spots in this inglorious list. With iOS being famed for its security, especially because of its closed source nature, this ranking will come as a major blow to the company and to staunch Apple fans as well. But is there a specific reason behind Apple’s disastrous security breaches? We take an in-depth look at that in the latter part of this article.
For now, we focus our attention on the other members of this list. Microsoft has done well itself as both Internet Explorer, and various versions of Windows have become more secure compared to the previous year. Adobe Systems Incorporated (NASDAQ:ADBE) finds its flash player and related plugins amidst a host of security issues. This is however not that big of a problem because the entire IT sector is on a slow yet steady migration towards HTML 5.
The one result that will raise the most eyebrows though, is the fact that Android, popularly knows as the more vulnerable smartphone OS has a significantly less number of threats compared to iOS. In fact, the number of vulnerabilities on iOS has more than doubled from 120 in 2014 to 375 in 2015, a 212.5% increase.
A few things to keep in mind while reading the report:
- Windows OS versions are counted separately probably because of their market share while Mac OS X is grouped together.
- The Linux Kernel vulnerabilities are listed separately from the Linux distributions because it can be updated separately.
- This list is compiled by the number of publicly known vulnerabilities and is as such not an accurate measure of how safe a software is.
Is Apple The New Target For Hackers?
Now there is a difference between vulnerabilities and hacks. This stems from the fact that because of Apple’s strict vetting of the app ecosystem in their stores, not many apps with malware or shady actions gets past them. However, with that being said, recent reports suggest that as much as 40% of Apple apps have potential vulnerabilities, and that can be a cause for concern.
Traditionally, Android has been targeted by most hackers, and with good reason as well. With 84.7% of the worldwide smartphone mark in their grasp, it’s easy to see why hackers will try to target Google’s OS. The same holds true for Windows in the Desktop space. As majority players, they are the primary target for hackers and cyber criminals and despite having a smaller number of vulnerabilities, they have more malware and viruses designed to exploit them.
Why Apple Has Come to the Forefront of the Security Scene
This graph clearly shows that cumulatively Apple, Adobe and Microsoft have the highest number of vulnerabilities in their software. Microsoft has had a tough time historically with bugs and vulnerabilities, and Adobe Flash is now a legacy product. However, Apple’s 181.18% YoY increase in vulnerabilities cannot be attributed to one single cause. We have outlined a few major causes that we think are responsible for hackers to have turned the spotlight on Apple in 2015.
- Amid a slumping PC market, Apple’s MacBook lineup has shown steady growth, a feat that has surely attracted the attention of hackers and malware creators.
- Windows 10 left the traditional and most outdated Internet Explorer and switched to a much more powerful and secure Edge browser. Added to that is the fact that Windows 10 is a free upgrade for all Windows 7,8 and 8.1 users and hackers have had a tough time dealing with the more secure and harder to crack the software.
- Apple Pay has got off to a great start, and this means that in the coming months, there will be more people who will be associating their phones with credit cards and other bank details. This has started a new wave of attacks as hackers renew their efforts to steal personal information off iPhones.
- There is a slew of Apple users running on older dated hardware that don’t have all of the latest software features from the latest iOS. As Apple looks to proliferate into budget markets, the problem will get worse and more hackers will join the fray trying to target the dated devices.
The Major Security Breaches at Apple In The Recent Past
In the recent past, Apple has been at the centre of some major hacks where Apple users have had sensitive private information stolen from either their iPhones or some other part of the Apple ecosystem. We have briefly highlighted a few of the major ones in here.
- iCloud Celebrity Hack: In late September of 2014, a group of hackers managed to gain access to the personal files and images of celebrities who had entrusted their intimate secrets by uploading them to iCloud.
- Apple ID Hack: Although this was only seen in jailbroken devices, one of the major reasons that this garnered attention was due to the sheer number of users that were affected, with the tally reaching nearly 220,000.
- XCode Ghost Hack: No doubt the biggest one of the year so far, this malware found it’s way inside the Apple app store piggybacking on various apps and managed to embed itself inside almost 40 popular apps from the App Store.
This shows that even the closed walls of Apple’s ecosystem has been breached, and something needs to be done to combat this growing menace.
Final Words
Highlighting a problem is important in its own right, but that’s only half the job done. As analysts, we strive to get to the cause of every problem and find solutions that can be implemented by the industry. Because while Apple may be the highlight of this article, the menace of fraudulent apps is one that is plaguing the entire smartphone industry as a whole.
While we have discussed in depth what can be done from the app developer’s and publisher’s point of view, today we would like to take a different look at the same problem. Here are some of the best practices that product developers and consumers can follow for keeping their data safe on the internet.
- Enabling biometric security in more applications from a native OS level and adding biometric scanners such as fingerprint sensors to their devices. This is one of the common trends that we saw in most of the flagships of the current year. We hope that it penetrates into the lower and mid-range segment as well.
- Ensuring that Two Step Authentication is the default mode of security in cases where sensitive information is stored.
- As for the consumers, public awareness about security goes a long way. Using a dedicated password manager, that can make passwords that are impenetrable to social engineering and brute force attacks can go a long way.
There has been a significant surge in hacks and vulnerabilities in the recent past as the total number of software flaws of the top 3 companies from last year was 524 flaws from Microsoft, followed by Oracle (465) and Apple (407). This year the numbers are significantly higher with Apple having 1147 flaws while Adobe and Microsoft both have more than 1.5k flaws each.
Industry experts believe that there will be more to follow as Symantec said,
Should Apple continue to grow in popularity, it seems likely that these trends will continue.
It remains to be seen that what Apple can do to combat the new threat to the iOS ecosystem. Will the bug-bounty systems be able to keep the hackers at bay? Only time will tell!