In an ongoing battle to protect its users, Google, the tech giant under Alphabet’s umbrella, has been waging war against thousands of malicious apps infiltrating its Play Store. Despite their efforts, hackers are finding crafty ways to exploit Google’s defences and steal users’ personal and financial information. In a recent report by Pradeo, two spyware apps hiding on the Google Play Store have affected up to 1.5 million users. Surprisingly, these file management tool apps were discovered not only compromising users’ devices but also secretly sending sensitive data to China.
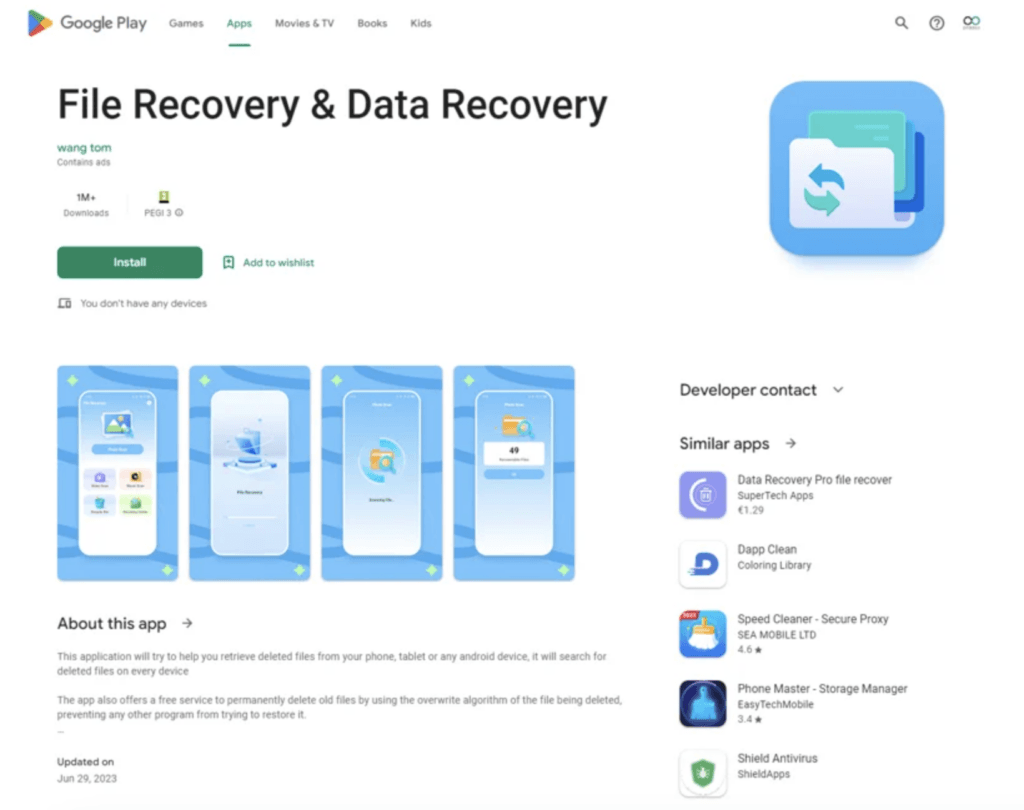
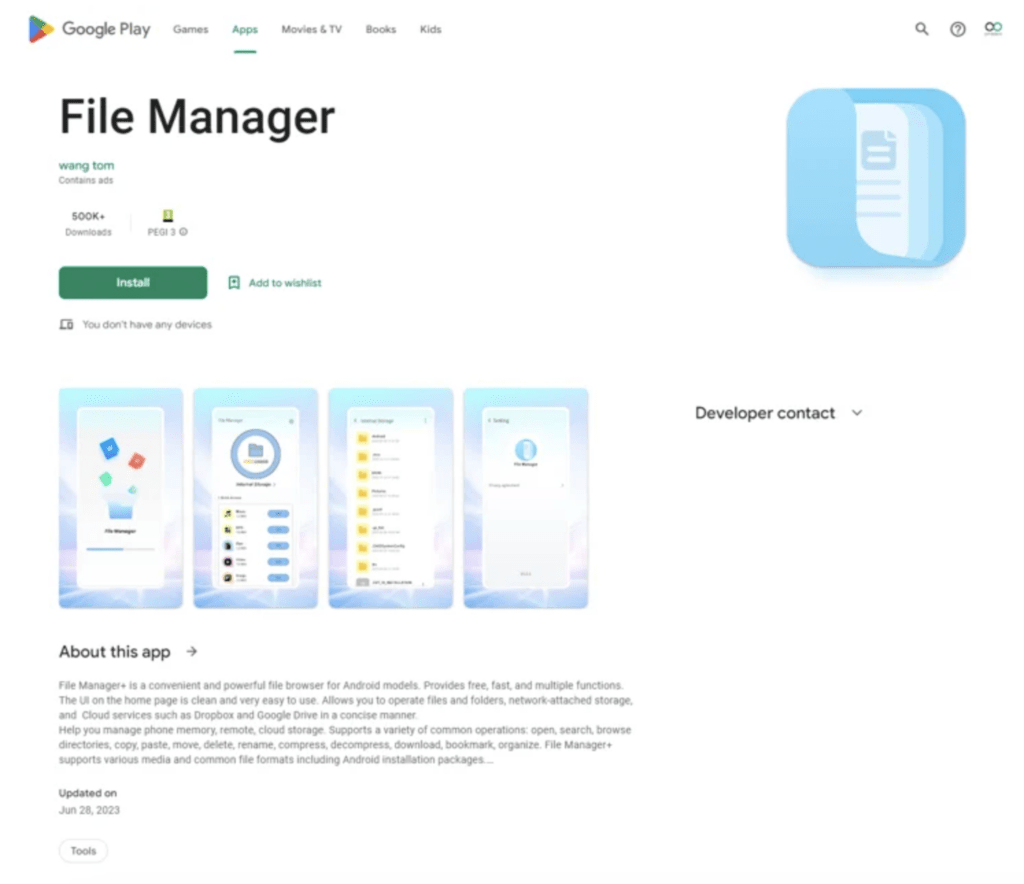
These two malicious Android apps are “File Recovery and Data Recovery” and “File Manager”. File Recovery and Data Recovery, operating under the alias com.spot.music.filedate, have over 1 million user downloads on the Google Play Store, while File Manager, operating under the alias com.file.box.master.gkd, has more than 500,000 installs.
The mastermind behind these 1.5 million data thefts is the same developer responsible for two suspicious apps. Both apps originate from the publisher known as wang tom.
Android Apps Steal Information
Designed to launch stealthily and without user interaction, the two popular Android apps named “File Recovery and Data Recovery” and “File Manager” are quietly sending their users’ sensitive data to malicious servers in China. The stolen data include:
- Users’ contact lists, extracted from the device itself and all connected accounts, such as email and social networks.
- Media files stored within the application, including pictures, audio, and video content.
- Real-time user location information.
- Mobile country code, indicating the user’s country of residence.
- Network provider name, revealing the cellular network service provider.
- Network code of the SIM provider, specifying the specific SIM card being used.
- Operating system version number, which can potentially expose vulnerabilities similar to the Pegasus spyware incident.
- Device brand and model information.
Pradeo’s analysis reveals that both applications conduct an unusually high number of data transmissions, exceeding a hundred instances. Such a large volume of data transfers is rarely observed, indicating an alarming level of data exfiltration. This further emphasizes the severity of these spyware applications and the urgency of taking measures to protect your personal information from their malicious activities.
After detecting this illicit behaviour, Pradeo immediately alerted Google.
As the threat of malicious apps continues to evolve, how can users remain vigilant and protect themselves from potential risks? What steps can individuals take to ensure the apps they download are safe and trustworthy?
Safeguarding Against Malicious Apps: Best Practices
We strongly recommend that all Android smartphone users check whether the apps “File Recovery and Data Recovery”, and/or “File Manager”, are installed on their devices. If you discover any of these two apps on your smartphone, it is crucial to promptly uninstall them. Taking immediate action to remove these apps will help safeguard your personal data and mitigate potential risks associated with their presence.
Here are a few additional security recommendations to minimize potential risks associated with downloading unfamiliar or untrustworthy applications:
For individuals:
- Exercise caution when downloading applications that have no user reviews despite claiming to have a large number of downloads. It is generally safer to opt for apps with positive user feedback and reviews.
- Take the time to read and consider user reviews when available. They often provide valuable insights into the true nature and reliability of the application.
- Before granting permissions to an app, carefully review and understand the access it requests. Be cautious if the permissions seem excessive or unrelated to the app’s functionality.
For organizations:
- Raise awareness among your employees about mobile threats and the importance of mobile security. Educate them about the risks associated with downloading and using unverified or suspicious applications.
- Implement automated mobile detection and response systems to ensure a secure and flexible environment for your users. These systems can evaluate applications against your organization’s security policy, preventing the launch of non-compliant or potentially malicious apps.
In a Nutshell
As the number of Android smartphone and app users continues to soar worldwide, the threat of falling into the clutches of hackers looms ominously. Google, ever vigilant, is leaving no stone unturned in its mission to safeguard users from downloading malicious apps from the Play Store. In October 2022, Google took decisive action by removing 16 Android apps that had adversely affected a staggering 20 million users.
Additionally, in April 2022, Google introduced its privacy-focused “nutrition labels” for apps. This initiative aimed to ensure that Google Play remains a safe and trusted space for users to enjoy the latest Android apps. These labels place a greater emphasis on the responsible handling of user data, allowing developers to disclose if they adhere to best practices in data security.
With the vast popularity of Android devices and the Play Store, Google is acutely aware of the risks posed by malicious apps. Their unwavering commitment to user safety drives continuous efforts to counter these threats head-on.
How do you think Google and users can work together to create a safer app environment? Share your thoughts in the comment section!

