DDoS attacks are on the rise yet again. The recent report by Verisign indicates the worrisome scenario as there has been a 35% increase reported in the number of DDoS attacks during Q2 2018 as compared to the previous quarter. What is even more concerning is the fact that 62% of those who experienced the DDoS attack in Q2 2018, were targeted multiple times.
The other major point of concern in the report is the type of attacks; about 52% of all the DDoS attacks in Q2 2018 utilised multiple attack types. According to the Q2 2017 DDoS attack report, the figure was an alarming 74% last year. Although, When compared to the same time last year, it was observed that there was a relative increase of a whopping 111% in the average of attack peak sizes.
One of the statistics maintaining its consistency over the course of the year is that the types of DDoS attacks. The figures this year point out that about 56% of all DDoS attacks were User Datagram Protocol (UDP) floods. This pretty much replicated the figures from the report a year back, where the UDP floods made up 57% of the DDoS attacks. Other major DDoS attack types include TCP based attacks and IP fragment attacks.
DDoS Attacks Q2 2018: Major Industries Targeted
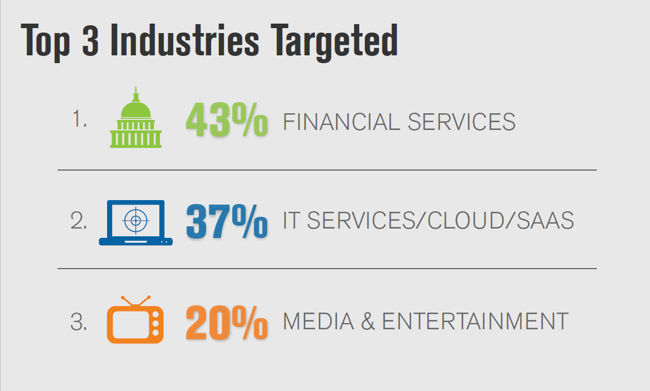
The industry of financial services managed to make it as the most targeted industry of DDoS attacks. It represented about 43% of the mitigation activity. However, the gap between the first and second place wasn’t that much either, unlike the gap exhibited by the Q2 2017 report. The IT/Cloud/Saas services finished a close second, accounting for about 37% of the mitigation activity. The third major industry targeted then was, in fact, the media and entertainment industry. They represented a significant 20% of the mitigation activity.
This represents a major shift in both the point of attack and the concentration of the same when compared to the same report in Q2 2017. The IT/Cloud/SaaS industry which was at the prime targeted for DDoS attacks last time has apparently taken measurable steps to prevent such attacks. The efforts apparently paid off and the percentage of targeted decreased from 55% to 37% this quarter. Consequently, attackers shifted their target from IT/Cloud/SAAS Industry to the Financial Services Industry and the target share of the industry went up from 31% to 43% in just one year.
The other major affected industry was, in fact, that of e-commerce and online advertising. They made up for about 13% of the mitigation activity.
The Biggest DDoS Attacks
Verisign observed quite a few DDoS attacks over the course of the quarter. Among them, the largest attack, volumetrically speaking, was a User Datagram Protocol (UDP) fragment flood. The flood peaked at approximately 42 Gigabits per second (Gbps) and 3.5 Million packets per second (Mpps). It lasted a total of about three hours. However, the biggest attack in terms of intensity was reported in a multi-vector attack which peaked at approximately 38 Gbps and 4.7 Mpps.
Final Words
After analysing the report and comparing it with its previous variant released about a year back, it is safe to say that the DDoS attacks are indeed shifting their focus away from the highly secured IT/Cloud/SaaS industry to the less tech-savvy financial industry. The increase in the number of attacks but the decrease in average peaks point towards increasingly frequent but less qualitative attacks. With the increase in pervasive manoeuvres against these attacks, the DDoS attacks might even cease to become a problem in the future. Till then, let’s hope for the best.
How to Avoid Such Attacks
These attacks usually do not fiddle with the data, but it can highly obstruct the functioning of an app or a website or a server. Therefore, it is highly important to keep a check on these attacks. Following steps can ensure the least impact from these attacks:
- Identifying a DDoS attack as early as possible is the first and one of the most important steps.
- Over-provisioning the bandwidth is another step for controlling DDoS attacks. Over-provisioning doesn’t exactly stop a DDoS attack, but it gives enough time to act before the site gets flooded.
- If a user has its own server, defending at network perimeter can be helpful in mitigating the effects of such attacks.
- Finally, the victim should take help from the ISP or hosting provider or even a DDoS specialist.
There are several tools available which can be helpful in preventing DDoS attacks and protecting your company. Some of these tools are Cloudflare, F5 Networks, Black Lotus, Arbor Networks and Incapsula.

