With more than 1.3 million activation each day, Google Inc (GOOG) Android has become the world’s most widely used Smartphone platform. As a result, despite being primarily designed for Smartphones and Tablets it has seen more applications in many fields. Though, it has proved itself as the widely used open mobile OS, yet it does have some loopholes when it comes to fight malware. Android malware infections found to have tripled in 2012 – increased by 163% compared to the base year.
Malware – A Brutal Reality of Google Android
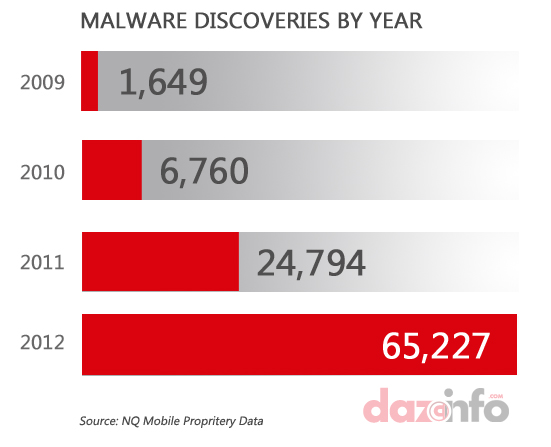
According to latest NQ Mobile Security report, 65,227 new pieces of mobile malwares were detected in 2012 – 163% increase compare to 2011. Unfortunately, Google Android remained the biggest target as 94.8% malwares were designed to attack on Android devices. Consequently, more than 32.8 million Android devices were infected last year which is three times more compare to 2011.
While many Android users root their device in order to enjoy early upgrade of OS, these users are easy target for malware infections. Around 65% of malwares detected in 2012 took places in the form of spyware, unauthorized rooting, pervasive adware and Trojan.
The prime goal of these malwares were to capture users’ personal data and information and get benefited out of that by using in the form of email marketing, SMS marketing, designing personalized campaigns based upon users’ activities and likeness. Around 28% malwares detected in 2012 were designed to trigger such unauthorized activities while 7% were designed only to jeopardize users’ experience by pushing the mobile for sudden death, reboot or to make it stop working.
How Malwares Are Being Delivered
The most common methods to broadcast malwares were identified as App Repackaging, Malicious URLs and Smishing.
App Repackaging works like ‘code injection’ where malware authors will alter the code of third-party apps, repackage it and upload on various third-party App Stores with identical name. Once installed on users devices, the code works in background and keep supplying users’ personal information and usage habits to malware authors.
Malicious URL is the most common trick on mobile and even on PCs. Such hackers will gain access to users’ personal or financial information by sending them to identical looking financial institution website but with hidden url. Once a user enters his personal information to log-in, it gets saved in malware authors database which would be used later to gain access to user’s account.
Smishing is used to trigger an act that attracts cost for mobile user. Activities like download premium music, tones, images or app are the real examples of this. Attackers trick user to click on a particular url or app icon and the download will start in background without having user’s concern.
Why Android
The biggest challenge for Google’s Android is its openness. Though, it’s a crucial aspect for mobile makers which get extended customization flexibility, but also being the easiest entry point for Malwares. Besides, majority of Android users are still hanging with 2 yrs old Gingerbread version. According to Google latest released figures Gingerbread still controls the biggest pie of Android with 39.8% market share. This has kept users away from many crucial updates designed to counter latest and upgraded malwares.
Another biggest reason behind Android target is the age-factor. In US 58% of children aged 13 – 17 own smartphone. The generation is known as an early adopters of technology and they tend to download more apps compare to other age groups. This attracts the risk of getting many infected apps coming from unauthorized sources or third-party market place where majority of malwares apps are hosted.


The only devices that have malware are those devices that are not running at least Ice Cream Sandwich or newer. It is NOT Google’s fault. The fault lies within the mobile carriers. They are the ones that are screwing the consumer.