In last one decade online crime has increased drastically. Hackers and online thieves have made many illegitimate attempt in an exponential rate. Unfortunately, still no such software or tool kit have been intercepted in internet world to catch them and they are moving freely.
In a recent incident, one of the Twitter user, named as Mr. Shoaib Ahmed, has found of selling credit cards online. In his tweet he has mentioned that “CVV Fullz unchecked Dumps all countries: Best CVV & VCC seller”. This line directly indicates that he is trying to sell active credit cards to users illegitimately. This indicates that now online miscreants are leveraging over social networking sites to advertise their deeds.
Shoaib used to sell credit card info, which is most likely collected with key-loggers from infected home computers. This means that somehow he managed to get hold of computers and got their credit card information while users attempted to do any online transaction and used to key-in their credit card information using the physical keyboard.
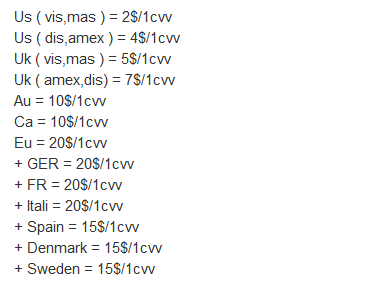
He has fixed the prices of stolen credit card and it range from $2 to $20. The cost of credit card mainly depends upon the country from where it is stolen.
Below table will provide you clear idea about rate chart:-
Here the term “vis” stands for visa, “mas” for Master Card, “dis” for discovery and “amex” for American Express Cards.
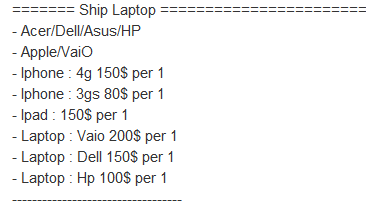
One of the best offers which he provides is that if users don’t want to purchase the stolen credit card then they can tell him to buy the products like iPhone, iPads and laptops on behalf and ship it to them. In the process he will log on to an online store and will deliver it to the specific address. Currently an iPad, bought like similar fashion, goes for $150.
Below is the list of table which highlights the price charged according to the stuffs:-
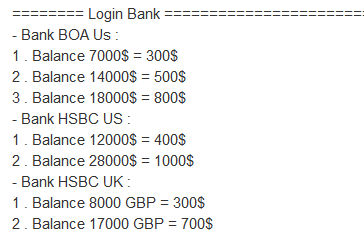
Online thieves also sell the access of bank accounts to other. Here, again, Keyloggers plays an important role to collect the password which users use to login into their bank account online. He charges according to the money in the account; for example for an account with $28,000 balance he charges $1,000.
Below table will provide clear idea about charges:-
Finally he posts information about some credit card user which includes address, victim name, credit card number, and password. However, while the verification process, information found to be incorrect.
The mix use of technology has become painful for many users who are not well-versed with its functionality, usability and protection. Users with basic knowledge and limited set of use are prime target by hackers. However, there are coupe of precautionary steps which could be taken to stay safe from all such unwelcome situations:
- Never use public or friend’s computer for any online financial transaction or activity.
- Try to avoid the use of physical keyboard as much as possible while key-in your credit card or account login information. Generally, all banks provide virtual keyboard ( on-screen Keyboard) as an optional mode to enter your account credentials.
- Expose your sensitive information only on pages protected by ‘Server Security layer’, also known as SSL. To ensure you can see an additional “s” after http://…… (https://…….)
- Perform Google Search every fortnight to cross information about yourself. Enter your name and trigger search. See if there is any private/sensitive information related to you has been crawled by Google bots.
Hope the above mentioned case study and instructions might help users in protecting themselves from online miscreants. Have you come across any such things or experience one by yourself ? If so, please share your with us and also tell us how much this report has helped you.




simply..speechless..shame on these people..